Just before the holidays, several high-ranking officials at San Juan College in Farmington, New Mexico, received urgent e-mails from the college president that said the president was in a meeting with fundraisers and needed them to hop online and buy $500 gift cards, scan the cards so their codes were visible and reply with the scans attached.
Or at least the e-mails appeared to come from the president. In fact, the e-mail address belonged to scammers who intended to use the gift card codes for their own thieving purposes. Unfortunately, one of the recipients followed their instructions.
“Our president doesn’t send those kinds of messages,” says Edward DesPlas, executive vice president at San Juan. Yet the recipient figured, “This is highly unusual, but if the president wants it, they’re going to get it.” But others alerted the information technology department, which sent out an e-mail asking people to ignore the requests. “This is an anecdotal situation of something that was pulled off by dealing with human weakness, and people’s desire to please the boss,” he says.
Editor’s note: This excerpt comes from the current issue of the Community College Journal, published by the American Association of Community Colleges.
Community colleges aren’t quite as high on the list of hackers and scammers as institutions like banks, hospitals and four-year research universities, yet the institutional and personal data stored on their servers and in the online cloud can be valuable, so they need to lock down their data like any other entity. This requires a combination of technological defenses like firewalls and encryption, along with training for faculty, staff and students so they recognize phishing and social engineering attempts to hack into their systems.
“Believing that it can happen to us, and fearing that, is probably the first thing you have to have in order to be proactive,” DesPlas says. “You’ve got to believe, ‘We will be under attack at some point,’ and you’ve got to believe, ‘It can happen to us.’ You’ve got to believe it is our responsibility to guard against the loss of data. It’s all about the attitude from the top.”
And at San Juan, President Toni Hopper Pendergrass helps set the tone.
“As we all know, information and personal identities seem to be the new currency,” Pendergrass says. “It is critical that we safeguard them as fervently as we do cash, equipment and other assets. In essence, they require Fort Knox levels of security and protection.”
Setting the tone
Indeed, the college president needs to set the tone, says Steven Hernandez, chief information security officer at the U.S. Department of Education.
“If protecting information technology is in the college’s strategic plan and part of the president’s talking points, that puts everyone on notice that it’s a priority,” he says. “The president needs to have an ongoing dialogue with the (chief information officer), (chief technology officer) and certainly the (chief information security officer) as we’re moving new technologies into the organization, and maybe move things onto the cloud. Every one of those is an opportunity to enhance security, in addition to improving the user experience.”
Related stories: Developing apprenticeships for cybersecurity and Training, testing are key to cybersecurity
Community colleges need to take cybersecurity as seriously as they take physical security issues, says Lee Petry, director of the Workspace One SET Team, government, education and healthcare, at cloud computing company VMWare. “If there is an active shooter on campus, there are policies, and you’ve trained your students and staff. What do you do for your data?” he says. “Have you updated your plan? What is your plan to secure your data? Do you have firewalls up? Do you have password protection? More often than not, there is no plan.”
James Henningsen, president of the College of Central Florida in Ocala, says two-year colleges need a culture in place that understands the importance of data protection at the highest levels and throughout the management team. “The culture has got to be set by the president,” he says.
Executives need to ensure that the right policies and procedures as well as communication channels are in place to keep up with cybercriminals, Henningsen says. “Hackers are developing new strategies every day, and security people are developing countermeasures every day,” he says. “We disseminate our message through governance groups. It’s important to get the word out. You can send stuff in an e-mail, but not everybody is going to read it. You’ve got to do multiple communication channels, and you need real-world examples.”
The president and CIO need a free, honest channel of communication about not only successes but also challenges and shortcomings, says Henry Glaspie, CIO at College of Central Florida. “Dr. Henningsen is very supportive in saying to me, ‘We have this problem, we don’t have the expertise, can I engage a third party so we can have those resources and skills on the ground?’”
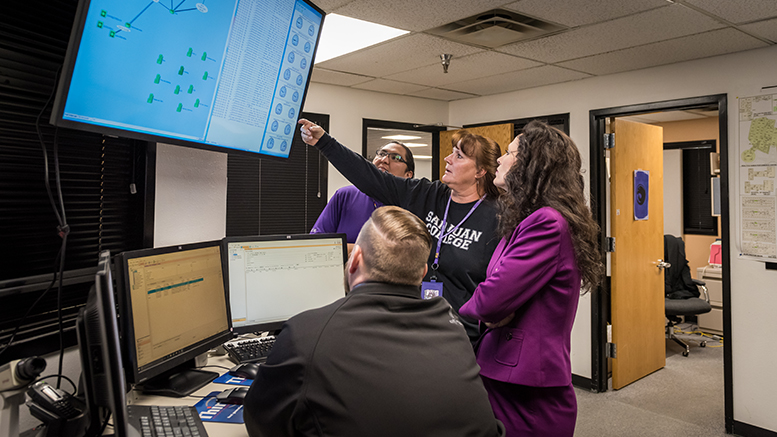
DesPlas says San Juan College engages in collaboration among departments from information technology to student services to administrative services to achieve the necessary combination of technological solutions — like next-generation firewalls and added protection against malware and ransomware — as well as “almost perpetual training, almost perpetual readiness drills” to ensure people have the right mindset. “We all have to know the first and last line of defense is the people we have working for us,” he says.
Laramie County Community College (LCCC) in Wyoming works to ensure broad, high-level communication about any potential cyber-dangers to students or employees, CTO Chad Marley says.
“We like to go to the president’s cabinet and make sure they’re informed,” he says. “We want to make sure everybody is aware of the risks.”
The college also has strengthened password policies, added encryption services to e-mail, implemented new training software, leveraged existing tools in the Microsoft campus environment and then some.